Ransomware’s Global Threat
Exploring the devastating impacts of ransomware on critical infrastructure and the urgent need for collective cybersecurity action.

Ransomware’s Global Threat: Lessons from Major Cyber Incidents
Ransomware has evolved from a niche extortion scheme into a powerful weapon capable of paralyzing essential services worldwide. High-profile incidents have demonstrated how a single unpatched vulnerability can cascade into chaos across sectors like healthcare, finance, and logistics. This article delves into the mechanics of these attacks, their profound repercussions, and actionable steps for mitigation in an increasingly interconnected digital landscape.
The Rise of Ransomware as a Disruptive Force
Once primarily a method for criminals to demand payments from individuals, ransomware now targets large-scale operations. Malicious software encrypts vital data, rendering systems inoperable until a ransom is paid—often in cryptocurrency. The shift toward disruption over mere profit signals a dangerous escalation, where attackers aim to sow confusion and economic damage.
Key drivers include the persistence of outdated software in critical systems and inadequate cybersecurity hygiene. Organizations reliant on legacy infrastructure face heightened risks, as exploits targeting known flaws remain effective due to delayed updates. This vulnerability window allows rapid propagation, turning isolated infections into global crises.
Case Studies: WannaCry and Beyond
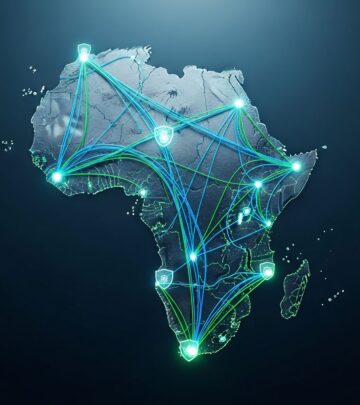
The 2017 WannaCry outbreak exemplified ransomware’s destructive potential. Exploiting a flaw in Microsoft Windows, it infected over 200,000 computers in 150 countries within days. Hospitals in the UK’s National Health Service halted surgeries and diverted ambulances, while factories and telecoms ground to a halt.
- Healthcare Impact: Patient records became inaccessible, delaying treatments and endangering lives.
- Transportation Disruptions: Airlines and shipping firms faced operational shutdowns, stranding cargo and passengers.
- Financial Strain: Banks suspended services, eroding public trust and causing economic ripple effects.
Subsequent attacks like NotPetya amplified these lessons, masquerading as ransomware but primarily designed for data destruction. Originating in Ukraine, it spread globally, costing billions and underscoring how geopolitical tensions can fuel cyber mayhem.1
Unpacking the Technical Vulnerabilities
At the core of many ransomware successes lies the exploitation of unpatched software. EternalBlue, the Windows SMB protocol vulnerability weaponized in WannaCry, was disclosed months earlier but not universally fixed. This highlights a systemic issue: the lag between vulnerability discovery and deployment of patches.
| Vulnerability Type | Examples | Exploitation Method |
|---|---|---|
| Software Flaws | Windows SMB, Adobe Flash | Remote code execution |
| Phishing | Email attachments | Social engineering |
| Weak Backups | No offline copies | Data encryption without recovery |
Beyond patching, poor backup strategies exacerbate damage. Without segmented, air-gapped backups, victims often pay ransoms or suffer permanent data loss. Attackers also leverage ransomware as a diversion for deeper intrusions, such as data exfiltration or lateral movement within networks.
Government and State Actor Involvement
Attribution challenges complicate responses, as nation-states sometimes stockpile vulnerabilities for offensive use rather than disclosing them. This practice undermines global security, prioritizing espionage or sabotage over collective defense.2
Responsible disclosure norms urge prompt sharing of flaws with vendors for patching. Governments should lead by example, ensuring critical infrastructure operators prioritize updates and resilience. International frameworks, like those from the World Bank, emphasize capacity-building against cybercrime, advocating legal harmonization and technical cooperation.3
Building Resilience: Best Practices for Organizations
- Prioritize Patching: Automate updates for all systems, testing in staging environments to minimize disruptions.
- Implement Multi-Layered Defenses: Use endpoint detection, network segmentation, and zero-trust architectures.
- Robust Backup Protocols: Follow the 3-2-1 rule—three copies, two media types, one offsite.
- Employee Awareness: Train against phishing via simulated attacks and clear reporting channels.
- Incident Response Planning: Conduct regular drills and maintain vetted third-party support.
Critical sectors must incorporate redundancy, such as failover systems, to maintain operations during attacks. Collaboration via Information Sharing and Analysis Centers (ISACs) accelerates threat intelligence sharing.
The Broader Economic and Societal Toll
Ransomware’s fallout extends beyond immediate victims. The 2017 attacks alone inflicted damages estimated in tens of billions, with cascading effects on supply chains. Healthcare delays can lead to loss of life, while port closures disrupt global trade.4
Reputationally, breached entities face prolonged recovery, customer attrition, and regulatory penalties. Economically, small businesses often fold post-attack, highlighting disproportionate impacts on under-resourced players.
Future Outlook: Evolving Threats and Countermeasures
As attackers refine tactics—employing fileless malware or supply-chain compromises—defenses must adapt. Emerging tech like AI-driven anomaly detection offers promise, but requires ethical implementation to avoid false positives.
Global standards bodies advocate for secure-by-design principles in software development, minimizing vulnerabilities from inception. Public-private partnerships are vital, pooling resources for vulnerability research and rapid response.
FAQs on Ransomware Defense
- What is ransomware?
- Malware that encrypts files or locks systems, demanding payment for restoration.
- How can I protect my organization?
- Patch promptly, backup rigorously, train staff, and segment networks.
- Should I pay the ransom?
- Experts strongly advise against it, as it funds crime and offers no recovery guarantee.
- Who is behind major attacks?
- Often criminal groups or state actors; attribution relies on cybersecurity forensics.
- What role do governments play?
- They must promote disclosure, regulate critical infrastructure, and cooperate internationally.
In conclusion, ransomware demands a unified front. By addressing patching delays, enhancing disclosures, and fostering collaboration, we can fortify the digital ecosystem against these pervasive threats.
References
- Enhancing Resilience Against Botnets and Other Automated, Distributed Threats — National Institute of Standards and Technology (NIST). 2018-05-30. https://csrc.nist.gov/csrc/media/publications/white-paper/2018/05/30/enhancing-resilience-against-botnets–report-to-the-president/final/documents/eo_13800_botnet_report_-_finalv2.pdf
- Stemming the Exploitation of ICT Threats and Vulnerabilities — United Nations Institute for Disarmament Research (UNIDIR). 2019-11. https://unidir.org/files/2019-11/stemming-the-exploitation-of-ict-threats-and-vulnerabilities-en-805-2.pdf
- Combatting Cybercrime: Tools and Capacity Building — World Bank Group. 2022 (updated). https://openknowledge.worldbank.org/bitstreams/39a137ff-0642-5f14-9a21-29a4f0eec8aa/download
- A Report to the President on Enhancing the Resilience of the Internet and Communications Ecosystem — NIST (related botnet resilience). 2018. https://csrc.nist.gov/csrc/media/publications/white-paper/2018/05/30/enhancing-resilience-against-botnets–report-to-the-president/final/documents/eo_13800_botnet_report_-_finalv2.pdf
Read full bio of medha deb