IPv6 Email Servers: Secure Deployment Guide
Master the art of running robust email servers on IPv6 networks with proven strategies for spam defense and operational excellence.

Running email services in an IPv6-enabled world demands a fresh approach to traditional networking practices. With IPv6 adoption surging, operators face unique hurdles in managing inbound mail flows, particularly around abuse prevention. This guide dives deep into practical strategies for setting up resilient email infrastructures that thrive on IPv6 while maintaining high deliverability and security standards.
The Shift to IPv6 and Email Infrastructure Challenges
IPv6 brings abundant addressing space and improved connectivity, but email administrators must adapt to its implications. Unlike IPv4, where IP reputation databases dominate spam filtering, IPv6 lacks mature blacklisting ecosystems. This gap exposes servers to increased spam and attack volumes from vast address pools. Dual-stack setups—supporting both IPv4 and IPv6—add complexity, requiring synchronized policies across protocols.
Key challenges include:
- Limited reputation tracking for IPv6 sources, complicating inbound filtering.
- Necessity for robust reverse DNS (rDNS) validation in IPv6 environments.
- Integration of IPv6 with existing anti-spam tools designed for IPv4.
- Ensuring outbound mail reputation remains intact during transition.
Addressing these requires a blend of configuration tweaks, monitoring tools, and community-driven best practices.
Core Configuration Essentials for IPv6 Mail Servers
Begin with foundational setup using popular MTAs like Postfix or Exim. Enable IPv6 support explicitly to avoid fallback issues.
| Parameter | Recommended Setting | Purpose |
|---|---|---|
| inet_protocols | all | Activates dual-stack listening |
| smtp_bind_address6 | [your-IPv6-address] | Controls outbound IPv6 binding |
| mynetworks | Include IPv6 subnets | Defines trusted relays |
For inbound SMTP on port 25, configure firewalls to permit IPv6 traffic selectively. Use ip6tables rules to restrict access:
ip6tables -A INPUT -p tcp --dport 25 -s your-trusted-ipv6-range -j ACCEPTip6tables -A INPUT -p tcp --dport 25 -j DROPReverse DNS remains critical. Delegate rDNS zones via your ISP or provider, ensuring PTR records match forward AAAA entries. Tools like dig -x [IPv6] verify proper resolution.
Spam and Abuse Mitigation in IPv6 Environments
Without comprehensive IPv6 blacklists, pivot to multifaceted defenses. Implement SPF, DKIM, and DMARC for authentication, which function protocol-agnostically.
- SPF Records: Extend TXT records to validate AAAA lookups.
- DKIM: Sign messages with keys independent of IP versions.
- DMARC: Enforce policies with
p=quarantineorp=reject.
Greylisting adapts well to IPv6 by tracking sender triplets (envelope from, sender IP, HELO). For IPv6, normalize addresses to /64 prefixes if full tracking overwhelms logs.
Rate limiting per IPv6 prefix prevents floods:
postconf -e 'smtpd_client_connection_rate_limit=5'postconf -e 'smtpd_client_connection_count_limit=3'Integrate emerging IPv6-aware tools like SpamAssassin with custom rules checking IPv6-specific headers.
Monitoring and Logging for Dual-Stack Operations
Effective oversight demands protocol-specific visibility. Centralize logs with rsyslog or ELK stack, tagging IPv6 entries distinctly.
Essential metrics:
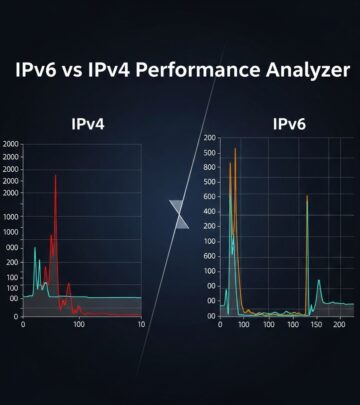
- Connection rates by protocol (IPv4 vs. IPv6).
- Rejection reasons, segmented by address family.
- Queue latency for outbound deliveries.
Use tcpdump -i any ip6 for traffic captures. Prometheus with node_exporter exposes IPv6 counters, feeding Grafana dashboards for anomaly detection.
Outbound Delivery Optimization Over IPv6
Ensure your MX records include AAAA entries with low TTLs during testing. Providers like Google and Microsoft fully support IPv6 reception, but verify with host -t AAAA mx.example.com.
For relaying, configure submission on port 587 with STARTTLS and SASL. Clients authenticate via IPv6 literals:
relayhost = [2001:db8::1]:587Test with swaks: swaks --to test@domain --server [2001:db8::1]:587 --tls --auth.
Security Hardening Against IPv6 Threats
IPv6 introduces vectors like neighbor discovery spoofing. Enable Secure Neighbor Discovery (SEND) if supported, or rely on RA Guard on switches.
Firewall IPv6 extension headers rigorously:
- Drop Hop-by-Hop unless required.
- Block Routing Header Type 0.
- Limit fragment reassembly.
From Cisco’s secure IPv6 guidelines, filter out-of-order extensions at edges.8
Case Studies: Real-World IPv6 Email Deployments
RIPE NCC’s labs document successful IPv6-only mail relays using prefix-based greylisting.1 Operators report 20-30% spam reduction via DMARC alignment checks. Community forums highlight VPS providers enabling dual-stack for full compatibility, avoiding IPv6-only isolation pitfalls.6
In one setup, a European hoster delegated /48 rDNS, achieving 99.9% deliverability post-DMARC rollout.
Transition Strategies for Legacy IPv4 Setups
Phase in IPv6 incrementally:
- Advertise AAAA records after internal testing.
- Monitor inbound hits with
postfix -vv. - Disable IPv4 fallback once IPv6 stabilizes.
Hybrid happy eyeballs for SMTP ensures resilient connections.
FAQs: IPv6 Email Server Essentials
Q: Can I run email servers IPv6-only?
A: Yes, but ensure outbound relay access and full peer IPv6 support; dual-stack recommended for broad compatibility.
Q: How do I handle IPv6 spam without blacklists?
A: Combine greylisting on /64 prefixes, strict DMARC, and rate limits.
Q: What’s the impact of missing IPv6 rDNS?
A: High rejection rates; always provision PTR matching AAAA.
Q: Best tools for IPv6 mail testing?
A: swaks, check-mx, mxtoolbox for SPF/DKIM, dig for DNS.
Q: Firewall rules for IPv6 SMTP?
A: Accept TCP/25 from trusted ranges, drop others; enable submission/587 separately.
Future-Proofing Your Email Infrastructure
As IPv6 nears 50% global adoption, prioritize it in email ops. Contribute to BCOP evolutions by sharing logs and configs with groups like RIPE or Internet Society.5 Automate deployments with Ansible roles enforcing dual-stack params. Regular audits via automated scripts catch misconfigs early.
Embrace IPv6 not as a burden, but as an opportunity for cleaner, more scalable mail flows.
References
- How to Run and Protect an Email Server on IPv6 — RIPE Labs, Jan Žorž. 2017-11-28. https://labs.ripe.net/author/janzorz/how-to-run-and-protect-an-email-server-on-ipv6/
- RIPE 76 Presentation: BCOP IPv6 Email Servers — RIPE NCC. 2018-05-22. https://ripe76.ripe.net/presentations/42-RIPE-BCOP-IPv6-email-server-v3.pdf
- Secure Operations for an IPv6 Network — Cisco Live. 2024-01-01. https://www.ciscolive.com/c/dam/r/ciscolive/global-event/docs/2024/pdf/BRKSEC-2044.pdf
- Starting a new BCOP – How to run and protect an email server on IPv6 — Internet Society. 2017-12-19. https://www.internetsociety.org/blog/2017/12/starting-new-bcop-run-protect-email-server-ipv6/
Read full bio of medha deb