IP Spoofing: A Persistent Threat Worth Tackling
Explore why IP spoofing remains a critical Internet vulnerability and the urgent need for global anti-spoofing measures to secure networks.

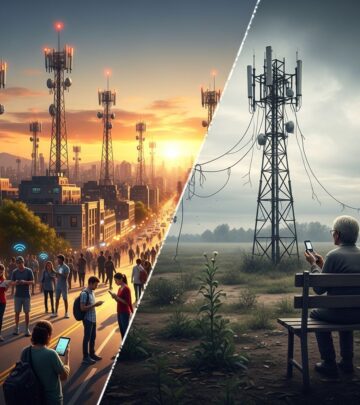
IP spoofing, where attackers falsify the source address in network packets, has long undermined the trustworthiness of Internet communications. This technique powers some of the most disruptive cyber incidents, particularly reflection-based Distributed Denial of Service (DDoS) attacks that overwhelm targets with amplified traffic. Despite decades of awareness, spoofed traffic continues to flow unchecked across vast swaths of the global network, posing risks to businesses, governments, and everyday users alike. Addressing this issue demands a blend of technical innovation, precise monitoring, and coordinated action among network operators worldwide.
The Mechanics and Dangers of Forged IP Addresses
At its core, IP spoofing exploits the Internet Protocol’s (IP) lack of built-in authentication for source addresses. A malicious actor crafts packets appearing to originate from a victim’s IP, tricking intermediary servers into responding to the victim instead. This is especially potent in amplification attacks, where small queries elicit large responses, multiplying the assault’s impact.
Reflection DDoS attacks, fueled by spoofing, have escalated in scale and frequency. Attackers scan for vulnerable services like DNS, NTP, or SSDP, sending spoofed requests that flood the target with replies. The collateral damage extends beyond direct victims, straining upstream providers and degrading service for innocents.
- Amplification Factor: Protocols like Memcached can amplify traffic by 50,000 times, turning modest inputs into gigabit floods.
- Attack Vectors: Beyond DDoS, spoofing aids session hijacking, man-in-the-middle exploits, and bypassing access controls.
- Real-World Impact: High-profile incidents have crippled financial institutions and cloud services, costing millions in downtime.
Without source validation, these threats persist, eroding confidence in the Internet’s foundational protocols.
Measuring the Scope: Tools Revealing Network Vulnerabilities
Quantifying IP spoofing’s prevalence is crucial for prioritizing fixes. Projects like the CAIDA Spoofer test networks by sending probes and assessing if spoofed packets escape. This initiative, ongoing since 2005, maps source address validation (SAV) adoption globally.CAIDA Spoofer Project data shows persistent gaps: as of recent measurements, over 50% of tested networks in many regions still permit outbound spoofing.
Other tools complement this:
| Tool/Project | Purpose | Key Insight |
|---|---|---|
| CAIDA Spoofer | Global SAV testing | 220+ countries; reveals edge network weaknesses |
| RIPE Atlas | Distributed measurements | Tracks prefix-level filtering efficacy |
| Shadowserver Scans | Inbound spoofing detection | Monitors bogon traffic propagation |
These measurements underscore that while core networks have improved, the ‘last mile’—customer-facing ISPs—lags, allowing spoofing to proliferate.
Technical Defenses: From BCP 38 to Advanced SAV
Best Current Practices (BCP) 38 and 84, published by the IETF, outline ingress and egress filtering to drop invalid packets at network borders.RFC 2827/BCP 38 recommends routers reject packets with source addresses not belonging to local prefixes. Yet, implementation remains spotty due to configuration complexity and legacy equipment.
More granular solutions include:
- uRPF (Unicast Reverse Path Forwarding): Validates packets by checking route tables; strict mode drops mismatches.
- SAVI (Source Address Validation Improvements): Binds IP-MAC-port combos in local segments, thwarting intra-network spoofing.
- RAV (Receive Authentication for Virtual Private Networks): Emerging for encrypted tunnels.
For small networks, default anti-spoofing in routers could yield quick wins. Data centers enforce tenant-isolated filtering, preventing prefix hijacks via BGP.
Barriers to Widespread Deployment
Why hasn’t spoofing been eradicated? Challenges span technical, economic, and human factors.
- Technical Hurdles: Asymmetric routing breaks strict uRPF; multi-homed setups complicate filters.
- Economic Disincentives: Operators bear filtering costs without immediate benefits, as attacks depend on collective action.
- Operational Resistance: Fear of blocking legitimate traffic deters aggressive filtering.
- Scale Issues: Millions of edge devices demand automated, zero-touch deployment.
Progress is uneven: North American and European core nets show high compliance, but Asia-Pacific and Africa trail, per Spoofer data.
Strategies for Global Mitigation
Tackling spoofing requires multi-stakeholder efforts. Voluntary initiatives like MANRS (Mutually Agreed Norms for Routing Security) commit operators to BCP 38 compliance.MANRS fosters peer pressure and shared incentives.
Regulatory nudges, such as EU directives or FCC guidelines, could mandate SAV for critical infrastructure. Incentives like reduced peering fees for compliant nets might accelerate adoption.
Research frontiers include AI-driven anomaly detection and blockchain-ledgered address validation, though scalability remains key.
The Cost-Benefit Imperative
DDoS damages exceed $100 billion annually, per industry estimates, dwarfing anti-spoofing investments. Unchecked spoofing risks Internet balkanization, as victims deploy blunt defenses. Proactive SAV preserves the open net while curbing abuse—a win for all.
FAQs on IP Spoofing and Defenses
What exactly is IP spoofing?
It’s forging the source IP in packets to impersonate another host, evading filters and enabling attacks.
How does spoofing fuel DDoS?
Spoofed requests to amplifiers redirect massive replies to victims, magnifying bandwidth exhaustion.
Is BCP 38 still relevant in 2026?
Absolutely; it’s foundational, with modern extensions like SAV building upon it.
Can individuals protect against spoofing?
Users benefit indirectly via ISP compliance; enable firewalls and use VPNs for added layers.
What’s the status of global SAV adoption?
Improving but incomplete; edge networks need focus, as shown by CAIDA metrics.
IP spoofing’s persistence signals a call to action. By leveraging measurements, enforcing standards, and building incentives, the community can forge a more resilient Internet.
References
- CAIDA Spoofer Project — CAIDA, UC San Diego. 2025-10-15. https://spoofer.caida.org/
- Network Ingress Filtering: Defeating Denial of Service Attacks which employ IP Source Address Spoofing (BCP 38) — IETF. 2000-05 (authoritative standard). https://datatracker.ietf.org/doc/html/bcp38
- Mutually Agreed Norms for Routing Security (MANRS) — Internet Society. 2024-03-12. https://www.manrs.org/
- Source Address Validation Improvements (SAVI) — IETF SAVI WG (archived). 2018-07. https://datatracker.ietf.org/wg/savi/documents/
Read full bio of Sneha Tete