IETF 101: Core Advances in DNS and Routing
Exploring pivotal IETF 101 sessions on DNS encryption, low-power routing, and IPv6 for constrained devices to shape the future Internet.
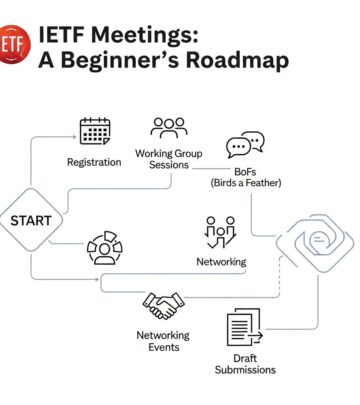
The Internet Engineering Task Force (IETF) remains the cornerstone of Internet protocol evolution, convening experts to refine the technologies that underpin global connectivity. At IETF 101, held in London, discussions zeroed in on critical areas like Domain Name System (DNS) security, routing protocols for resource-constrained environments, and IPv6 deployment in emerging networks. These sessions addressed real-world challenges, from privacy threats to scalable IoT integration, ensuring the Internet’s foundational layers evolve with modern demands.
Enhancing DNS Privacy with Encrypted Queries
DNS, often called the Internet’s phonebook, translates human-readable domain names into IP addresses. However, traditional DNS queries sent in plaintext expose user browsing habits to eavesdroppers, including ISPs and potential attackers. The DNS Over HTTPS (DoH) working group at IETF 101 focused on standardizing encrypted DNS transport over HTTPS, blending it seamlessly with web traffic.
DoH aims to protect against surveillance and tampering by encapsulating DNS messages within HTTPS. This approach leverages widespread HTTPS infrastructure, making it easier for browsers and apps to adopt without new ports or protocols. Key debates centered on a primary draft for DNS queries over HTTPS, balancing usability, performance, and privacy. Participants weighed interoperability with existing resolvers against the risks of centralization if major providers dominate DoH endpoints.
Benefits include reduced latency in mixed-traffic scenarios and mitigation of DNS spoofing. Challenges involve ensuring DoH doesn’t bypass network-level filtering intended for security. The session underscored the need for clear guidelines on endpoint discovery and fallback mechanisms to plain DNS when HTTPS fails.
Routing Challenges in Low-Power Lossy Networks
Routing Over Low power and Lossy networks (ROLL) tackled the complexities of directing traffic in environments like smart grids and industrial sensors. These networks feature devices with limited battery life, erratic links, and high packet loss, demanding lightweight protocols unlike those for data centers.
ROLL builds on IPv6 Routing Protocol for Low-Power and Lossy Networks (RPL), optimizing for metrics like energy efficiency and link quality. IETF 101 discussions advanced drafts on objective functions that prioritize paths based on constraints such as node rank and expected transmission count. A major focus was integrating RPL with 6LoWPAN for header compression, enabling full IPv6 stacks on tiny devices.
Real-world applications shone through: urban sensing deployments where RPL adapts to mobility, and agricultural monitoring with multi-hop topologies. Experts addressed scalability issues in dense networks, proposing loop prevention and distributed route computation. Security enhancements, like counter-based replay protection, were refined to counter physical tampering risks in deployed nodes.
| Protocol | Key Features | Use Cases | Challenges |
|---|---|---|---|
| RPL | Distance-vector, DODAG formation | Smart meters, home automation | High churn in mobile setups |
| LOADng | Reactive on-demand routing | Mesh networks, ad-hoc | Overhead in route discovery |
| PIM-SM | Multicast tree building | Group communication | State management in losses |
IPv6 Adaptation for Resource-Constrained Nodes
The IPv6 over Networks of Resource-constrained Nodes (6lo) working group bridged IPv6 to low-power personal area networks (6LoWPANs). Legacy IPv4 hacks no longer suffice as IoT explodes; 6lo compresses headers to fit 80-byte frames while preserving end-to-end connectivity.
IETF 101 highlighted adaptations for non-IP link layers like Bluetooth Low Energy (BLE) and NFC. Drafts progressed on 6lo over DECT-ULE for cordless phones and IEEE 802.15.4e TSCH for time-slotted channels. These enable IPv6 routing in subnetworks without translation, fostering native multihoming and mobility.
Performance metrics showed header compression reducing overhead by 90%, crucial for battery life. Discussions tackled fragmentation strategies for large IPv6 packets and neighbor discovery optimizations. Integration with ROLL was a hotspot, allowing seamless upward routing from 6lo backbones to the Internet core.
Operational Best Practices for DNS Resilience
The Domain Name System Operations (dnsop) session dissected day-to-day DNS management. Topics spanned query minimization to curb data leakage, response policy zones for malware blocking, and metrics for resolver health.
Operators shared war stories on DDoS mitigation, advocating rate-limiting and anycast deployment. A key draft proposed algorithms for root priming, ensuring resolvers fetch hints efficiently post-restart. Privacy emerged strongly, with calls to strip EDNS Client Subnet by default and prefer QNAME minimization.
Future-proofing included DNS over TLS (DoT) alongside DoH, providing encrypted options without browser dependency. The group emphasized testing frameworks like dns-zone-digest for integrity checks.
Integrating TLS Across Applications
Using TLS in Applications (UTA) extended encryption paradigms beyond HTTPS. Sessions explored TLS for DNS (DoT), NTP, and SSH, standardizing profiles for certificate validation and key exchange.
DoT drafts advanced with ALPN identifiers for multiplexing. Debates on opportunistic encryption versus strict mandates highlighted trade-offs in legacy environments. UTA pushed for post-quantum readiness, auditing cipher suites against emerging threats.
- TLS 1.3 Mandates: Enforced 0-RTT limits to prevent replays.
- Certificate Transparency: Logs for public audits.
- Key Rotation: Automated in long-lived sessions.
Interconnections and Broader Implications
These working groups interlink: DoH/DoT feed into dnsop privacy ops; 6lo underpins ROLL deployments. Collectively, they fortify the Internet against surveillance, scale IoT securely, and optimize routing for edge computing.
Outcomes from IETF 101 propel RFCs toward standardization, influencing browsers like Firefox and Chrome adopting DoH, and platforms like Thread using 6lo-RPL stacks. Challenges persist in adoption barriers—enterprise firewalls blocking HTTPS DNS, or power budgets in remote sensors—but momentum builds.
Stakeholders from operators to vendors collaborate, ensuring protocols remain open and evolvable. As 5G and edge roll out, these foundations enable secure, efficient connectivity at scale.
Future Directions and Open Questions
Looking ahead, IETF eyes DNS authentication evolutions like DNSSEC triggering, and RPL extensions for LPWANs like LoRaWAN. Privacy remains paramount: will DoH fragment the namespace? How to measure encrypted DNS uptake?
Routing faces AI-driven optimizations, predicting link failures via ML. 6lo must adapt to Wi-Fi 6 HaLow for longer ranges. dnsop pushes verifiable credentials in queries, blending blockchain-like proofs.
These evolutions demand inclusive participation, especially from Global South networks facing unique constraints.
Frequently Asked Questions
What is DNS over HTTPS (DoH)?
DoH tunnels DNS queries inside HTTPS packets, encrypting them to prevent snooping and enhance privacy.
How does RPL differ from traditional routing like OSPF?
RPL forms directed acyclic graphs suited to lossy links, unlike link-state protocols optimized for stable, high-bandwidth nets.
Why is 6LoWPAN important for IoT?
It shrinks IPv6 headers for tiny packets, enabling direct Internet access without NAT gateways.
Can DoH and DoT coexist?
Yes, DoT uses a dedicated port for system-wide encryption, while DoH suits app-specific privacy.
What are the power-saving features in ROLL?
Trickle timers slow updates in stable topologies, and rank-based forwarding minimizes transmissions.
References
- RFC 6550: RPL: IPv6 Routing Protocol for Low-Power and Lossy Networks — IETF. 2012-03. https://datatracker.ietf.org/doc/html/rfc6550
- RFC 8484: DNS Queries over HTTPS (DoH) — IETF. 2018-10. https://datatracker.ietf.org/doc/html/rfc8484
- RFC 4944: Transmission of IPv6 Packets over IEEE 802.15.4 Networks — IETF. 2007-09. https://datatracker.ietf.org/doc/html/rfc4944
- IETF 101 Meeting Proceedings — IETF. 2018-03. https://www.ietf.org/proceedings/101
- DNS Privacy Considerations — IETF Draft. 2023-05 (updated). https://datatracker.ietf.org/doc/html/draft-ietf-dprive-dnsoverhttps-usage-04
Read full bio of medha deb