Hidden Dangers of Encryption Weaknesses
Exploring how government demands for access to encrypted devices risk creating universal vulnerabilities that criminals can exploit worldwide.

In an era where personal data is the lifeblood of modern society, strong encryption stands as a critical shield against unauthorized access. Yet, recurring tensions between law enforcement needs and individual privacy rights continue to test this foundation. Governments worldwide have sought ways to pierce these protective layers, often framing such efforts as necessary for public safety. This push raises profound questions about the long-term consequences of tampering with cryptographic safeguards. While the intentions may stem from legitimate investigative requirements, the fallout can extend far beyond any single case, potentially exposing billions of users to heightened risks.
The Core Conflict: Security vs. Access
At the heart of this debate lies a fundamental clash. Encryption technologies, such as those embedded in smartphones, ensure that only authorized users can access sensitive information. Advanced passcode protections and auto-erase features prevent brute-force attacks, where hackers repeatedly guess credentials until success. Law enforcement agencies, however, argue that in criminal investigations—particularly those involving terrorism or serious crimes—these features hinder justice. Requests for companies to modify software for specific devices highlight this tension, blurring the line between targeted assistance and systemic vulnerability creation.
Consider the mechanics involved. Modern devices employ layered defenses: hardware-based secure enclaves store encryption keys, while software enforces delays between failed login attempts. Disabling these for one unit could theoretically unlock critical evidence. But the real peril emerges when such modifications reveal exploitable patterns or tools that adversaries might replicate or steal.
Historical Precedents and Their Lessons
One pivotal episode unfolded in 2016, when U.S. authorities compelled a major tech firm to alter its operating system for a locked device linked to a tragic event. The firm resisted, citing risks to all users, as any custom tool could theoretically be repurposed for mass exploitation. This wasn’t about handing over an existing key; it involved engineering a new bypass mechanism, effectively crafting a digital skeleton key.
Fast-forward to recent developments. In 2025, UK regulators issued notices under investigative powers legislation, demanding adjustments to cloud encryption services from the same company. Such actions underscore a pattern: initial requests for ‘one-off’ help often evolve into broader policy demands. These cases illustrate how legal orders can pressure firms into compromising their core security promises.
- Targeted device unlocks set precedents for wider mandates.
- Custom software risks leakage through hacks or insider threats.
- Global interoperability means local changes affect international users.
Technical Realities of Building Bypass Tools
Creating a software variant to circumvent protections isn’t trivial, but it’s feasible for developers familiar with the codebase. For instance, removing passcode retry limits allows automated cracking tools to succeed rapidly. Installing this on a device requires physical access, but once done, it neutralizes safeguards. The issue compounds if the tool’s existence becomes known—malicious actors could demand similar modifications or exploit stolen versions.
Moreover, end-to-end encryption in messaging and storage relies on mathematical certainty: without the private key, data remains gibberish. Introducing scanning mechanisms, as proposed in some child safety initiatives, involves on-device analysis that matches content against databases. While marketed as privacy-preserving, these systems create new attack surfaces. An adversary gaining control of the scanning logic could pivot to detect arbitrary data, undermining the ‘end-to-end’ guarantee.
| Feature | Standard Protection | With Bypass |
|---|---|---|
| Passcode Retries | Limited with delays | Unlimited brute-force |
| Auto-Erase | Deletes data after failures | Disabled |
| Encryption Keys | Hardware-protected | Software-accessible |
| Impact Scope | Device-specific | Potentially universal |
Broad Implications for User Trust and Innovation
Trust forms the bedrock of technology adoption. When users learn that their devices harbor government-mandated weaknesses, confidence erodes. Companies invest heavily in security to differentiate products; undermining this stifles innovation. Developers might hesitate to deploy cutting-edge cryptography, fearing future compelled disclosures.
Economically, the stakes are immense. A single breach exploiting a mandated flaw could cost billions in damages and lawsuits. National security suffers too: weakened civilian tools become prime targets for state-sponsored hackers, compromising military communications and infrastructure if similar standards apply.
Global Dimensions of the Encryption Debate
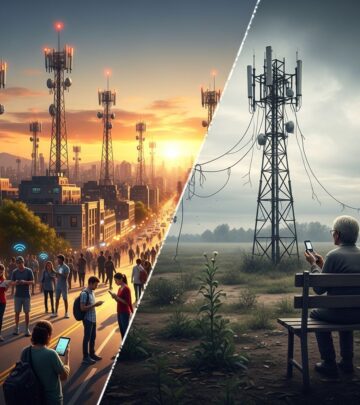
Encryption transcends borders. A vulnerability crafted in one nation ripples worldwide due to software universality. Authoritarian regimes could cite democratic precedents to justify their own demands, pressuring firms for universal backdoors. International standards bodies emphasize that robust cryptography bolsters collective defense against cyber threats.
Balanced approaches exist, such as key escrow systems where governments hold recovery keys under strict oversight. Historical attempts, however, reveal flaws—keys get lost, stolen, or misused. Metadata access, warrants for stored data, and advanced forensics offer alternatives without gutting protections.
Voices from Experts and Organizations
Cryptography pioneers have long cautioned against deliberate weaknesses. Bodies like the Electronic Frontier Foundation argue that even ‘narrowly scoped’ scans invite abuse: tweak parameters, and surveillance expands. Official reports from standards organizations reinforce that no backdoor remains narrow forever.
Industry leaders echo this: refusing such requests preserves integrity. Public discourse, not secret orders, should shape policy. Transparent debates involving technologists, policymakers, and civil society yield sustainable solutions.
Alternatives to Weakening Encryption
Rather than compromises, viable paths forward include:
- Enhanced Forensics: Invest in non-invasive tools like signal intelligence and behavioral analysis.
- Legal Reforms: Streamline warrants for voluntary data handover where feasible.
- International Cooperation: Share threat intelligence without universal access mandates.
- User Education: Promote secure habits like strong passcodes and backups.
These prioritize safety without sacrificing privacy.
Future Outlook: Toward Resilient Standards
As quantum computing looms, post-quantum encryption will demand even stronger commitments. Policymakers must weigh short-term gains against enduring risks. A world with reliable encryption fosters free expression, secure commerce, and resilient societies.
Frequently Asked Questions
What exactly is an encryption backdoor?
A backdoor is any method that allows unauthorized access to encrypted data, bypassing normal authentication. It can be deliberate code or an exploitable flaw.
Does helping law enforcement once create a precedent?
Yes, single instances often lead to repeated demands, eroding security norms over time.
Are there safe ways to balance privacy and security?
Options like metadata analysis and legal data requests preserve encryption’s integrity while aiding investigations.
How does this affect everyday users?
Weakened devices heighten risks of hacking, identity theft, and surveillance for all.
What role do international laws play?
Harmonized standards prevent a race to the bottom in security practices.
References
- A Message to Our Customers — Apple Inc. 2016-02-16. https://www.apple.com/customer-letter/
- Encryption Under Threat: The UK’s Backdoor Mandate and Its Impact on Online Safety — Internet Society. 2025-05. https://www.internetsociety.org/blog/2025/05/encryption-under-threat-the-uks-backdoor-mandate-and-its-impact-on-online-safety/
- Apple’s Plan to ‘Think Different’ About Encryption Opens a Backdoor to Your Private Life — Electronic Frontier Foundation. 2021-08. https://www.eff.org/deeplinks/2021/08/apples-plan-think-different-about-encryption-opens-backdoor-your-private-life
- Encryption: We must say no to back doors — World Wide Web Foundation. 2016-02. https://webfoundation.org/2016/02/encryption-we-must-say-no-to-back-doors/
- Investigatory Powers Act 2016 — UK Government (gov.uk). 2016 (amended 2025). https://www.legislation.gov.uk/ukpga/2016/25/contents
Read full bio of medha deb