Digital Connectivity and Protection in a Globalized Internet Landscape
Balancing worldwide connectivity expansion with cybersecurity imperatives

The rapid expansion of internet connectivity worldwide presents both remarkable opportunities and significant challenges for the international community. As more individuals, businesses, and governments become integrated into the digital ecosystem, the imperative to maintain security while fostering open access has become increasingly complex. This examination explores the multifaceted relationship between universal connectivity goals and the protective mechanisms necessary to ensure a trustworthy internet environment for all users.
The Evolution of Global Internet Infrastructure
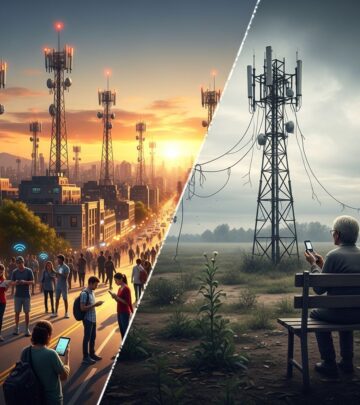
Over the past two decades, internet penetration has transformed from a privilege available only to developed nations into an essential utility for billions of people across every continent. The infrastructure supporting this growth encompasses undersea fiber optic cables, terrestrial networks, satellite systems, and mobile networks that collectively form the backbone of modern communications. However, this expansion has not proceeded uniformly across regions, creating digital divides that reflect broader economic and developmental disparities.
The deployment of internet infrastructure requires substantial capital investment, technical expertise, and coordinated governance structures. Developing nations face particular challenges in acquiring the necessary resources and knowledge to establish competitive digital networks. Meanwhile, developed countries continue to invest in high-speed connections and emerging technologies that further the gap in digital capability. This uneven development creates vulnerabilities in the global network, as weaker infrastructure in certain regions can become vectors for security threats that affect the entire interconnected system.
Security Imperatives in an Interconnected Environment
The open nature that makes the internet valuable for communication and commerce simultaneously creates vulnerabilities that malicious actors can exploit. Cyber threats have evolved from isolated incidents affecting individual users to coordinated attacks that can disrupt critical infrastructure, compromise national security, and cause substantial economic damage. The borderless nature of cyberspace means that vulnerabilities in one region can quickly impact systems and users worldwide.
Critical Infrastructure Protection
Modern societies depend on interconnected systems for essential services including power generation and distribution, water treatment, transportation networks, and healthcare delivery. These critical infrastructure systems increasingly rely on internet-connected components to optimize operations and reduce costs. However, integrating legacy industrial systems with networked digital infrastructure creates security challenges that engineers and policymakers continue to grapple with. A successful cyberattack against energy infrastructure, for example, could leave millions without power, disrupt supply chains, and cause cascading failures across multiple sectors.
Data Privacy and User Protection
As internet usage expands, individuals generate unprecedented volumes of personal data through their online activities. This information, aggregated and analyzed by both commercial and state actors, creates privacy concerns that governments have only begun to address through legislation. The collection and use of personal data raises fundamental questions about user autonomy, consent, and the balance between personalization benefits and privacy erosion. Different cultural and legal frameworks have emerged in response, ranging from comprehensive privacy regulations to lighter-touch approaches that prioritize innovation over protection.
Building Trust in Digital Systems
Effective internet governance requires establishing trust mechanisms that allow users to confidently engage in online transactions and communications. Encryption technologies, digital certificates, and authentication protocols form the technical foundation of this trust infrastructure. However, the relationship between security technologies and law enforcement objectives has created ongoing tension between those advocating for strong encryption and governments seeking access to encrypted communications for investigative purposes.
The establishment of reliable identity verification systems online remains an unsolved challenge in many contexts. Without robust mechanisms to verify that users are who they claim to be, online fraud flourishes and legitimate transactions become difficult. Various approaches have emerged, from biometric authentication to blockchain-based identity verification, each presenting distinct advantages and limitations regarding security, privacy, and accessibility.
Policy Framework Considerations
Governments and international organizations have attempted to establish policy frameworks that simultaneously promote connectivity and security. These efforts must navigate competing interests from multiple stakeholders including telecommunications companies, technology providers, civil liberties organizations, law enforcement agencies, and national security apparatus. The resulting policies often represent compromises that satisfy no constituency completely but attempt to address legitimate concerns from multiple perspectives.
International Cooperation and Standards
The technical standards that govern internet functionality exist in a complex landscape of official standards bodies, industry consortia, and de facto standardization through dominant implementations. International coordination on security standards, encryption protocols, and data protection requirements helps ensure that security measures function effectively across borders. However, disagreements about appropriate security levels, privacy protections, and government access create ongoing tensions in establishing consensus on technical standards.
Regulatory Approaches Across Jurisdictions
Different nations have adopted varying approaches to regulating internet services and protecting users. Some jurisdictions have implemented comprehensive data protection regulations that require explicit user consent for data collection and provide individuals with substantial rights regarding their information. Others have taken lighter regulatory approaches, allowing market forces to shape privacy protections. Still other nations have implemented restrictive regulations that give governments substantial authority to monitor online activities, often in the name of national security or social stability.
Emerging Technologies and Their Security Implications
New technologies that enhance connectivity also introduce novel security challenges. The Internet of Things encompasses billions of connected devices that were not designed with robust security in mind, creating vast attack surfaces that malicious actors can exploit. Artificial intelligence systems trained on large datasets can perpetuate biases while simultaneously becoming targets for adversaries seeking to manipulate their outputs. Cloud computing architectures centralize data and services in ways that create both efficiency benefits and concentration of risk.
5G Networks and Connectivity Expansion
Fifth-generation wireless technology promises substantially faster data speeds and lower latency than previous generations, enabling new applications from remote surgery to autonomous vehicles. However, the increased connectivity that 5G provides also expands the potential for cyberattacks and surveillance. The concentration of infrastructure in fewer network components creates single points of failure that could have widespread consequences if compromised. Additionally, concerns about the security of equipment from certain manufacturers have become a significant geopolitical issue affecting infrastructure deployment decisions.
Balancing Openness with Security Measures
A fundamental tension exists between the aspirations for an open internet where information flows freely and security imperatives that require monitoring, filtering, and controlling access to certain content or services. Pursuing complete openness without security protections leaves users vulnerable to fraud, malware, and exploitation. Implementing comprehensive security measures, however, can enable government censorship, corporate surveillance, and restriction of access to information. Navigating this balance requires ongoing dialogue among stakeholders with legitimate but sometimes conflicting interests.
The Role of Encryption
Encryption technologies serve as essential tools for protecting sensitive communications and data from unauthorized access. They enable secure financial transactions, protect medical records, and allow dissidents in restrictive environments to communicate without state surveillance. However, widespread encryption also prevents law enforcement from intercepting communications of criminal or terrorist organizations, creating pressure on governments to mandate backdoors or weaken encryption standards. Technical experts generally agree that weakening encryption for law enforcement purposes would necessarily weaken security for all users, but this technical reality conflicts with security agency preferences for investigative access.
Content Moderation and Information Control
Internet platforms increasingly play a role in moderating content, removing material that violates community standards or applicable laws. This moderation activity intersects with free expression principles in complex ways, particularly when different jurisdictions have conflicting standards regarding what content should be restricted. Private platforms exercise substantial control over online discourse, raising questions about accountability and the appropriate scope of corporate power over public discourse.
Infrastructure Resilience and Redundancy
Building secure internet infrastructure requires redundancy and resilience mechanisms that allow services to continue functioning even when some components fail or come under attack. Geographic diversity of data centers, multiple pathways for network traffic, and backup systems reduce the impact of localized disruptions. However, implementing such redundancy increases costs substantially, creating pressure to minimize protective infrastructure. Balancing efficiency with resilience remains an ongoing challenge for infrastructure operators and policymakers.
Developing Equitable Access Solutions
Achieving truly global connectivity requires addressing the economic barriers that prevent billions of people from accessing the internet. This challenge extends beyond the costs of physical infrastructure to include device affordability, data plan expenses, and digital literacy requirements. Community-based solutions, public-private partnerships, and innovative business models have emerged in various contexts to address access barriers. However, ensuring that expanded access includes appropriate security protections and privacy safeguards requires integrating security considerations into these development efforts from inception rather than treating security as an afterthought.
The Evolving Threat Landscape
Cybersecurity threats continue to evolve as defensive technologies improve, creating ongoing challenges for those responsible for internet security. State-sponsored actors now represent significant threats alongside criminal organizations and individual hackers. Nation-states use cyberattacks as tools for espionage, infrastructure disruption, and information warfare. Meanwhile, the sophistication of criminal malware increases continuously, employing advanced evasion techniques and exploiting vulnerabilities discovered in widely-used software before developers can release patches.
Education and Digital Literacy
Technical security measures alone cannot adequately protect users who lack understanding of the risks inherent in online activities. Security awareness training, education about identifying phishing attempts, and promotion of good password practices represent essential components of a comprehensive security posture. However, reaching billions of people with effective security education presents logistical and resource challenges that existing approaches have not adequately addressed. The variation in literacy levels and technical sophistication across populations means that one-size-fits-all educational approaches often prove ineffective.
Future Directions and Collaborative Approaches
Addressing the complex intersection of global connectivity expansion and security requirements will require collaborative approaches involving governments, technology companies, civil society organizations, and international institutions. Solutions must balance competing interests while recognizing that perfect security and perfect openness represent unachievable ideals. Instead, progress toward acceptable compromises that improve both connectivity and security for users worldwide represents the realistic objective.
Continued investment in research examining the technical, policy, and governance dimensions of internet security and connectivity will help inform better decision-making. Dialogue among stakeholders with different perspectives and priorities, conducted with genuine commitment to understanding differing viewpoints, can help identify solutions with broader acceptance. As technology continues to evolve and internet usage expands into new domains, the challenge of maintaining secure and open networks will remain central to our digital future.
References
- Internet Society — Internet Society. 2016-01-29. https://www.internetsociety.org/blog/2016/01/2016-confronting-the-promise-and-the-challenge-of-a-global-open-internet-connection-and-security/
- Recommendation for Key Management: Part 1 – General — National Institute of Standards and Technology (NIST). 2019-01-21. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-57pt1r5.pdf
- Framework for Improving Critical Infrastructure Cybersecurity (Version 1.1) — National Institute of Standards and Technology (NIST). 2018-04. https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.04162018.pdf
- Worldwide Broadband Speed League — Cisco. 2024. https://www.cisco.com/c/en/us/solutions/collateral/executive-perspectives/annual-internet-report/white-paper-c11-742636.html
- Global Datasphere: Data Age 2025 — International Data Corporation (IDC). 2024-03. https://www.idc.com/getdoc.jsp?containerId=IDC_P8667
Read full bio of Sneha Tete