DNS Security and Privacy Advances
Exploring key developments in DNS protection and confidentiality from recent industry discussions and standards.

The Domain Name System (DNS) serves as the Internet’s phonebook, translating human-readable domain names into machine-readable IP addresses. However, its foundational design from the 1980s leaves it vulnerable to modern threats like data interception and manipulation. Recent conferences and standards bodies have spotlighted critical upgrades to bolster DNS integrity and user anonymity. This article examines these evolutions, from cryptographic validation to encrypted query protocols, and their implications for global connectivity.
Understanding DNS Vulnerabilities
Traditional DNS operates in plaintext, exposing queries to anyone on the network path. Attackers can exploit this through DNS spoofing, injecting false responses to redirect users to malicious sites, or via man-in-the-middle intercepts that log browsing habits. Such weaknesses not only compromise security but also erode privacy, as resolver operators and eavesdroppers gain insights into user behavior.
Statistics underscore the urgency: according to recent reports, unencrypted DNS traffic constitutes over 90% of queries in many networks, enabling widespread surveillance. High-profile incidents, including state-sponsored cache poisoning, highlight the need for robust defenses.
Fortifying DNS with Cryptographic Authentication
DNSSEC (DNS Security Extensions) introduces digital signatures to verify response authenticity. By establishing a chain of trust from root servers downward, it prevents tampering. Validators check signatures against public keys, rejecting forged data.
- Key Benefits: Eliminates spoofing risks and ensures data origin integrity.
- Implementation Challenges: Requires zone signing by domain owners and resolver upgrades.
- Adoption Metrics: As of 2023, over 30% of top-level domains support DNSSEC, per Verisign data.
Despite progress, full deployment lags due to operational complexity. Events like regional tech gatherings have urged operators to prioritize validation to mitigate amplification attacks.
Encrypting DNS Traffic for Confidentiality
While DNSSEC authenticates, it doesn’t hide queries. Protocols like DNS-over-TLS (DoT) and DNS-over-HTTPS (DoH) address this by tunneling traffic over secure channels.
| Protocol | Port/Method | Strengths | Limitations |
|---|---|---|---|
| DoT | TCP 853 | Low latency, native TLS encryption | Requires dedicated port; easier to block |
| DoH | HTTPS 443 | Blends with web traffic; firewall evasion | Higher overhead; centralization concerns |
DoT wraps queries in TLS, authenticating servers and encrypting payloads. DoH embeds them in HTTP/2 or QUIC, leveraging browser integrations like Firefox and Chrome. These shield against passive surveillance but demand client and server updates.
Privacy Enhancements Beyond Basic Encryption
Ongoing research targets resolver-authoritative server links, currently unencrypted. IETF efforts explore aggregate privacy metrics and query minimization, where resolvers send only necessary name parts upstream.
- Query minimization reduces leak exposure during recursion.
- Oblivious DoH (ODoH) adds proxy layers for metadata protection.
- Local root server mirrors cut external queries, boosting resilience.
These innovations promise end-to-end confidentiality, though authoritative server upgrades pose scalability hurdles due to computational demands.
Industry Initiatives and Collaboration
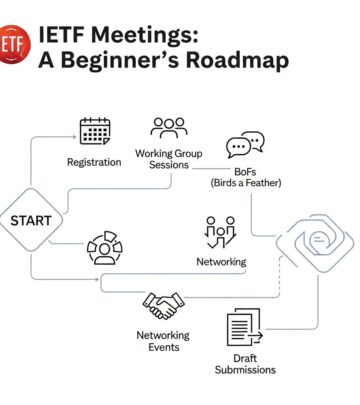
Conferences such as e-AGE have become hubs for DNS discourse, with organizations advocating flag days—coordinated upgrade events. DNS Flag Day 2020, for instance, tested EDNS0 compliance, vital for DNSSEC and extensions (RFC 6891).
Operators must handle oversized UDP packets or fallback gracefully. Collaborative testing revealed compliance gaps, spurring fixes. Similarly, IETF working groups like DPRIVE refine standards, transitioning experiments to full RFCs.
Challenges in Widespread Deployment
Transitioning to secure DNS faces hurdles: legacy systems resist change, and recursive providers hold query visibility, necessitating trust models. Centralization in DoH/DoT resolvers like Cloudflare raises monopoly fears.
Regulatory pressures vary; some regions mandate encryption, others block it citing censorship needs. Balancing usability, performance, and security remains key.
Future Directions in DNS Evolution
Emerging standards like DNS over QUIC promise faster, more reliable encryption. Hybrid models combining DoT/DoH with DNSSEC offer comprehensive protection. Expect increased focus on authoritative encryption and privacy-by-design in IoT devices.
Stakeholders urge metrics for measuring deployment success, such as encrypted query percentages tracked by APNIC and RIPE.
Practical Steps for Organizations
To enhance DNS posture:
- Enable DNSSEC validation on resolvers.
- Deploy DoT/DoH-capable clients and servers.
- Monitor for EDNS0 support and stale data serving (draft-ietf-dnsop-serve-stale).
- Participate in flag days and testing initiatives.
- Audit resolver logs for privacy compliance.
FAQs
What is the main difference between DNSSEC and DoH?
DNSSEC verifies data integrity via signatures; DoH encrypts queries over HTTPS for privacy.
Can DNS encryption slow down my Internet?
Minimal impact with modern hardware; QUIC variants reduce latency further.
Is DNSSEC backward compatible?
Yes, unsigned zones resolve normally, but signed ones require validation for full security.
Who controls major DoH resolvers?
Entities like Google, Cloudflare, and Quad9; users should choose trusted providers.
How do I test my DNSSEC setup?
Use tools like dnssec-analyzer.verisignlabs.com or dig +dnssec.
In summary, securing DNS demands layered approaches: authentication via DNSSEC, encryption through DoT/DoH, and privacy innovations. As threats evolve, collective action from developers, operators, and users will safeguard this cornerstone of the Internet.
References
- DNS Security Extensions (DNSSEC) — Internet Engineering Task Force. 2023-05-15. https://datatracker.ietf.org/doc/html/rfc9364
- DNS Privacy Considerations — Internet Society Deploy360. 2022-11-10. https://www.internetsociety.org/resources/deploy360/dns-privacy/intro/
- DNS over TLS (DoT) — Internet Engineering Task Force. 2023-01-20. https://datatracker.ietf.org/doc/html/rfc7858
- Extension Mechanisms for DNS (EDNS0) — Internet Engineering Task Force. 2013-04-15 (authoritative, still current standard). https://datatracker.ietf.org/doc/html/rfc6891
- Serving Stale DNS Data to Improve Resolver Performance — Internet Engineering Task Force. 2024-02-28. https://datatracker.ietf.org/doc/html/rfc9762
Read full bio of medha deb